- Can Mac Be Hacked Through Terminal 6
- Can Mac Be Hacked Through Terminal 5
- Can Mac Be Hacked Through Terminal 7
- Can Mac Be Hacked Through Terminal 2
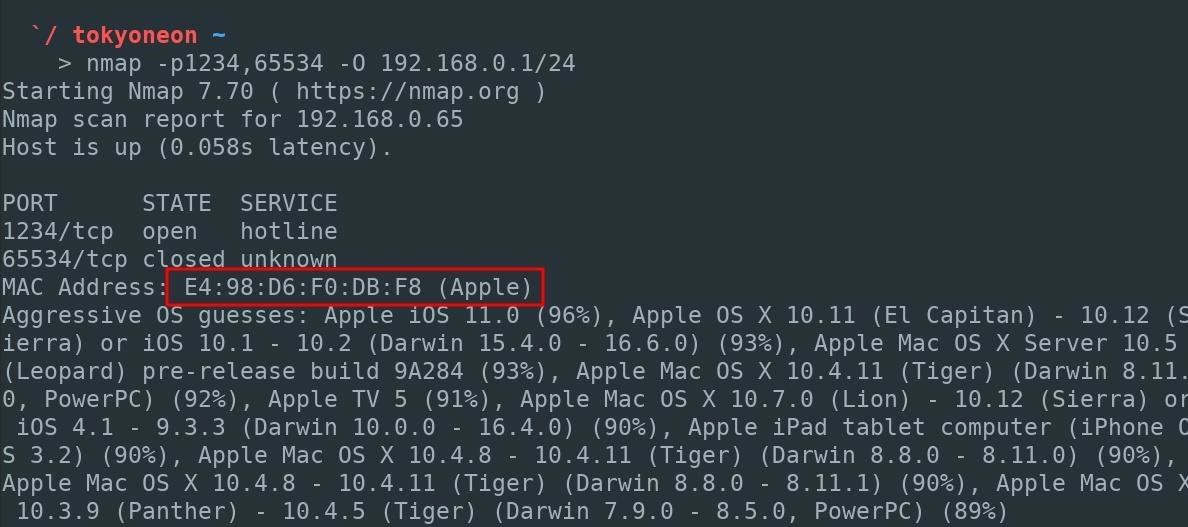
Can he break into my WI-FI Network by spoofing my MAC address, so the MAC filter in my router would let him through, because my neighbour would use spoofed MAC address of my tablet. How to avoid being hacked and how can I figure out that somebody hacked into my tablet or into my network. Any computer can be hacked if you are careless enough to permit it. There's nothing special about any computer in this regard. Getting hacked means you have put your computer onto the internet with no protection like a firewall or hardware router or you have allowed general access to the computer but do not have a sufficently strong enough password(s). Dec 09, 2017 Today, we're going to go over some great interface and user tweaks you can execute to customize your Mac. These tricks are often simple and can help you spruce up your Mac far beyond what the System Preferences window allows. So, without further ado, 15 great tricks you can execute in Terminal. Tweak the Finder.
You turn on your MacBook and feel that something is wrong: some files have disappeared, or new files were added. You wonder if someone has been watching your computer.
So, how to tell if someone is remotely accessing your MacBook? You need to check your logs, verify that no new users were created, make sure that remote login, screen sharing and remote management are disabled, and no spyware is running on your computer.
First things first. If you suspect that someone is controlling your laptop and if there is a chance that they watching you thru the webcam immediately apply a cover on laptop’s webcam. You can find my favorite webcam covers here.
What is remote access and how is it configured on MacBooks?
There are three ways to access MacOS remotely: allow remote logins from another computer, enable Screen Sharing or allow access by using Remote Desktop. Both ways are legitimate, but if you don’t remember doing any of them you need to know how to turn on and off those possibilities.
Can Mac Be Hacked Through Terminal 6
Remote login to MacOS
Computers that run MacOS as an operating system can log in to your Mac using Secure Shell (SSH). Steps to enable remote login are the following:
- Go to System Preferences. You can get there by clicking on the apple icon on the left of the top bar. After you clicked on apple icon you will see a drop-down menu where you should click on System Preferences menu item.
- Find Sharing folder and double click. Click on Remote Login checkbox on the left.
- Now you have the option to allow access either for all user or only specific users.
Once Remote Login is enabled then users with access can use SSH to log in and browse your computer’s contents.
Access to Mac screen using Screen Sharing
If you need help from IT to make changes on your MacBook or maybe you are collaborating on a project and want to share your screen you can enable Screen Sharing. Steps to enable as follows:
- Go to System Preferences.
- Find Sharing folder and double click. Click on Screen Sharing checkbox on the left.
- Allow access either for all user or only specific users.
Now on another Mac (from which you want to access to your Mac) start Screen Sharing app. You can start it by clicking Command and Space buttons. In a popup form type Sharing and hit Enter. Type your computer name. In my case, I had to type in “dev-pros-MacBook-Pro.local”.
A new window will pop up with the shared screen of another computer. Now you can control the screen.
Remote Desktop with Remote Management
Finally, it is possible to login to a computer with MacOS by enabling Remote Desktop. Steps to enable as follows:
- Go to System Preferences.
- Find Sharing folder and double click. Click on Remote Management check box on the left.
- Allow access either for all user or only specific users.
- There will be different Sharing options where you can fine-tune the type of access to allow: observe, change settings, delete, copy and even restart the computer.
Now you can access this Mac from Apple Remote Desktop – it’s an application you can buy from Apple Store and at the time of writing it’s cost was $79.99.
If your Mac is being monitored, it will show this image (two rectangles) in the top right-hand corner near your computer time:
When that symbol appears, you will be able to tell if you are being monitored. You can also disconnect the viewer by clicking on Disconnect option:
You can also click on “Open Sharing Preferences…” which will open Sharing folder in System Preferences.
Since the question you had was if someone remotely accessing your computer then the chances are that you don’t need any of sharing capabilities mentioned above.
In this case, check all options on Sharing folder under System Preferences to make sure that nobody is allowed to access it and turn off (uncheck) all options.
Verify if new users were created
As we’ve seen already remote login or sharing options require assigning access roles to the local users. If your system was hacked it is very likely that the hacker has added a new user to access it. To find out all users in MacOS perform the following steps:
- Start Terminal app by either going to Applications and then Utilities folder or clicking Command and Space and typing Terminal in the popup window.
- In the Terminal window type:
On my laptop it listed dev1, nobody, root and daemon.
If you see the accounts, you do not recognize then they probably have been created by a hacker.
In order to find when the user account was used to log in last time type the following command into the Terminal:
last
For each account, MacOS will list the times and dates of logins. If the login to any of the accounts happened at an abnormal time, it is possible that a hacker used a legitimate account to log in.
Check the logs
It may be useful to check the system logs for any possible access issues.
In order to find a system log, click on Go option in the top menu or simultaneously click Shift, Command and G. In the “Go to Folder” popup type: /var/log and hit Enter.
Now find system.log file and scan for word sharing. For instance, I found following screen sharing log entries:
These were log entries when someone logged in to my system remotely:
Check for spyware
If you are still suspecting that spyware is running on your machine you can use a third party application like Little Snitch which monitors applications, preventing or permitting them to connect to attached networks through advanced rules. Setting up the rules for Little Snitch, however, could be complicated.
One of the common spyware applications is a keystroke logger or keylogger. Keyloggers used to be apps that record the letters you type on the keyboard, but they significantly in last years. Suffice to day that keyloggers can take screenshots every 30 seconds or even track your chat activity, including the messages sent to you.
I believe that keyloggers are much greater security threat because they are easier to install and the powerful features they offer. Check my article about keyloggers here: How to know if my Mac has a keylogger
Security Best Practices
1.Change passwords regularly
One thing you should immediately if you are suspecting that someone is logging to your system is to change your password. And the password should be complex enough so that other people wouldn’t be able to guess it. This means avoiding using things like birthdate, first or last name or relatives, house or apartment number, etc. As a rule of thumb the password must be long enough (8 – 32 characters) and include at least 3 of the following character types:
- Uppercase letter (A-Z)
- Lowercase letter (a-z)
- Digit number (0-9)
- Special characters such as ~!@#$%^&*
2.Enable Security Updates by clicking on “Automatically keep my Mac up to date” in Software Update folder in System Preferences.
3. Install Antivirus. I received a lot of emails where people described suspicious activity on their Macs. I found that in about 60-70% cases, the culprit was malwareand not someone breaking into the computer. It’s a myth that Macs don’t get viruses. If you need proof check the next article I wrote after testing 12 antivirus programs after injecting 117 malware samples on my Mac:
Last Updated on
OS X's command line and I have never been what I'd call 'friendly'; rather, we have a mutual respect and understanding about not messing with each other. (Well, as much of a mutual respect as one can have between a human being and a code window.)
While the average person should never have any reason to visit Terminal, Apple's command line interface app actually does give you access to quite a few neat tricks and shortcuts... if you're willing to take a peek.
What is Terminal?
Apple's Terminal app is a direct interface to OS X's bash shell — part of its UNIX underpinnings. When you open it, Terminal presents you with a white text screen, logged in with your OS X user account by default.
Here's the important part: With a system administrator account and password, you have direct access to tweaking almost everything about your computer's software code; that means that while this little window provides great power, it comes with great responsibility. In short, be careful before using Terminal to execute commands, and make sure you understand what you're typing.
You can also use Terminal to securely connect to other machines, web servers, and even create your own scripts, but those are how-tos for another day. For now, we're going to focus on using Terminal to explore your own computer.
Basic Terminal commands you should know
Before we get started with the fun stuff, let's learn some basic Terminal terminology and commands. These form the framework for more complex interactions (aka, the fun stuff).
How to execute a Terminal command
You can type something in the Terminal window until you're blue in the face, but it won't execute until you press the Return key on your keyboard. At that point, it will either return an error if you've typed something incorrectly, or the command will execute.
Unless you're executing a command that requires the display of text in Terminal, you won't have any indicator that what you've done has been successful; you'll just get a new line with your user name on it once the command is finished processing.
When writing commands and paths in Terminal, almost everything is case sensitive: This means that you need to remember to properly capitalize 'Dock' when referring to the Dock, or OS X won't understand your command.
What's a path?
You can use Terminal to get direct access to your files without using the Finder. To do so, you build something called a path. Paths look similar in some ways to website sub-directories, and follow the structure of your folders.
Paths take two forms: absolute paths and relative paths. An absolute path starts at the root level of your hard drive, and is displayed as '/'. So if you wanted to make a path to your Applications folder, you would write '/Applications/'.
Relative paths are defined based on where you've already navigated to, and represented by './'. For instance, if you go to the '/Applications/' folder in Terminal, that's your current working directory (cwd). You can then get to your Utilities folder by typing './Utilities/' rather than '/Applications/Utilities'.
When you first launch Terminal, you're starting in the current working directory of /Users/myusername/ (also known as your User folder).
How to display and move between files in Terminal
To actually put all this path knowledge to use, you'll need the Terminal commands for displaying and changing files.
ls: The 'ls' command, by itself, displays the contents of the cwd. So if I were just to type 'ls' in Terminal, it would display the contents of my user directory:
You can optionally add an absolute or relative or path if you want to view a different directories. So, for example, if I wanted to view the Utilities folder inside Applications, I could type 'ls /Applications/Utilities/'. This won't change your current working directory, but it'll let you view other directories on your hard drive.
You can add options to view more information about that directory. The options for 'ls' include:
- -l, which lets you view the permissions of each file in the directory
- -R, which will not only show each folder in the directory, but all their files, as well
- -a, which will show any hidden files in the current directory
cd: Where the 'ls' command lets you view a directory, the 'cd' command will actually move to that directory (change your cwd). For instance, if after viewing the Utilities folder, you want to move to it, you'd type 'cd /Applications/Utilities/'.
pwd: Write this command by itself to help you remember the path of your current directory. When typed into terminal, it will print the full path of your cwd.
man: This command, followed by another Unix command, lets you read the Unix manual about the second command. This is super useful if you want to try a cool Terminal trick you found online, but aren't sure what those commands actually do.
For instance, typing 'man ls' will get you information on the 'ls' command, which lists directory contents.
How to modify files, folders, and preferences in Terminal
defaults: This command is often used in Terminal tips and tricks to tweak applications and system settings via their preference files. You can use it to do things like disable transparency in the menu bar, always show your scroll bars, change trackpad behavior, and much much more. You'll usually see this paired with either 'write' and a string, as with this:
The code above lets you save all your screenshots as JPGs instead of the system default PNG.
killall: If you execute a Terminal command that affects any system process or app, you're going to need to reboot the process to make it take effect. 'killall' followed by the process will do so. (This is also another way to force quit misbehaving apps or processes if your Force Quit menu isn't behaving.) Remember, this command and its target are case sensitive.
ln: OS X has long offered aliases, which let you create links to files, folders, and applications elsewhere in the system without having to duplicate them. Unfortunately, certain apps don't play well with aliases. With the link command 'ln -s', you can create a low-level, UNIX-based symbolic link which most system processes will recognize. Likely, you'll never have to make a symbolic link, but on the off-chance you want to perform a Terminal trick that requires them, this is how you do it.
The first path listed is your original file's path; the second path is where you'd like your symbolic link.
chflags: This commands lets you view and change the flags on a file or folder. For most people, the only flags you're going to care about are 'hidden' and 'nohidden', which hide and unhide documents, respectively.
sudo: If you spend any time online, you've probably heard of 'sudo' before. This is Unix's override command, and lets you execute any command as an administrator — provided, of course, that you have the requisite password and permissions. It probably goes without saying, but as a Terminal beginner, it's generally a good idea not to mess with commands like 'sudo' unless you are 100 percent sure what you're doing.
How to use Terminal for fun and whimsy
say: Feeling lonely? You can make your computer say anything you like with the 'say' command, and you can even record it in audio format to your desktop, if you so choose.
telnet towel.blinkenlights.nl: This isn't technically something local to your Mac, but it's my all-time favorite Terminal trick. Some kind soul on the internet made an all-ASCII version of Star Wars: A New Hope; run the following code, and you'll be treated to a full showing. If it doesn't make you smile just a little bit, you might be dead inside.
macOS Catalina
Can Mac Be Hacked Through Terminal 5
Main
We may earn a commission for purchases using our links. Learn more.
exposure notificationNational COVID-19 server to use Apple and Google's API, hosted by Microsoft
Can Mac Be Hacked Through Terminal 7
Can Mac Be Hacked Through Terminal 2
The Association of Public Health Laboratories has announced it is working with Apple, Google, and Microsoft to launch a national server that will securely store COVID-19 exposure notification data.